QUESTION 61
You have a computer that runs Windows 7. The Encrypting File System (EFS) key is compromised. You need to create a new EFS key. Which command should you run?
A. Certutil -GetKey
B. Cipher.exe /k
C. Lcacls.exe /r
D. Syskey.exe
Answer: B
Explanation:
Cipher
Displays or alters the encryption of folders and files on NTFS volumes. Used without parameters, cipher displays the encryption state of the current folder and any files it contains.Administrators can use Cipher.exe to encrypt and decrypt data on drives that use the NTFS file system and to view the encryption status of files and folders from a command prompt. The updated version adds another security option. This new option is the ability to overwrite data that you have deleted so that it cannot be recovered and accessed.When you delete files or folders, the data is not initially removed from the hard disk. Instead, the space on the disk that was occupied by the deleted data is “deallocated.” After it is deallocated, the space is available for use when new data is written to the disk. Until the space is overwritten, it is possible to recover the deleted data by using a low-level disk editor or data-recovery software.If you create files in plain text and then encrypt them, Encrypting File System (EFS) makes a backup copy of the file so that, if an error occurs during the encryption process, the data is not lost. After the encryption is complete, the backup copy is deleted. As with other deleted files, the data is not completely removed until it has been overwritten. The new version of the Cipher utility is designed to prevent unauthorized recovery of such data.
/K Creates a new certificate and key for use with EFS. If this option is chosen, all the other options will be ignored. By default, /k creates a certificate and key that conform to current group plicy. If ECC is specified, a self-signed certificate will be created with the supplied key size. /R Generates an EFS recovery key and certificate, then writes them to a .PFX file (containing certificate and private key) and a .CER file (containing only the certificate). An administrator may add the contents of the .CER to the EFS recovery policy to create the recovery for users, and import the .PFX to recover individual files. If SMARTCARD is specified, then writes the recovery key and certificate to a smart card. A .CER file is generated (containing only the certificate). No .PFX file is genereated. By default, /R creates an 2048-bit RSA recovery key and certificate. If EECC is specified, it must be followed by a key size of 356, 384, or 521.
QUESTION 62
You have a portable computer that runs Windows 7. The computer is configured to keep an offline version of files located in a network share.
You need to identify whether you are working on an offline version of a file.
What should you do?
A. From Sync Center, click View sync partnerships.
B. From Action Center, click View archived messages.
C. From Windows Explorer, select the file and then view the toolbar.
D. From Windows Mobile Device Center, click the Connection settings.
Answer: C
Explanation:
To find out whether you’re working offline: Offline files turn on automatically if you lose your network connection. A copy of your file is copied to your computer, and once your network connection is re-established, the two copies will be synchronized. To find out if you’re working offline, do the following.
1. Open the network folder that contains the file you are working on.
2. Check the Details pane at the bottom of the window for the status. If the status is offline, you are working with a copy of the file on your computer. If the status in online, you are working with the file on the network.
QUESTION 63
You have a computer that runs Windows 7.
You mark a folder as Always available offline.
You need to verify that an offline copy of the folder has been created on the computer. What should you do?
A. Open Sync Center and review the status.
B. Open Action Center and review any messages or issues.
C. Open Windows Mobile Device Center and review the status.
D. Open Network and Sharing Center and review the status for the local area connection.
Answer: A
Explanation:
What is Sync Center?Sync Center allows you to check the results of your recent sync activity if you’ve set up your computer to sync files with a network server. This allows you to access copies of your network files even when your computer isn’t connected to the network. Sync Center can tell you if the files synced successfully or if there are any sync errors or warnings.
NoteSync Center is designed to help you sync with files in network locations. If you want to sync a mobile device with your computer, such as a mobile phone or portable music player, Windows gives you several other options. You can install the sync software that some manufacturers include with their device, or you can use the new Device Stage feature in this version of Windows if your device supports this feature. For more information, see Sync music, pictures, contacts, and calendars with a mobile device.
QUESTION 64
Your company has a server that runs Windows Server 2008 R2. The server is configured as a remote access server. The external firewall has TCP port 80 and TCP port 443 open for remote access connections.
You have a home computer that runs Windows 7.
You need to establish secure remote access connection from the home computer to the remote access server.
Which type of connection should you configure?
A. IPSec
B. L2TP
C. PPTP
D. SSTP
Answer: D
Explanation:
Secure Socket Tunneling Protocol
Secure Socket Tunneling Protocol (SSTP) is a new form of VPN tunnel with features that allow traffic to pass through firewalls that block PPTP and L2TP/IPsec traffic. SSTP provides a mechanism to encapsulate PPP traffic over the SSL channel of the HTTPS protocol. The use of PPP allows support for strong authentication methods such as EAP- TLS. The use of HTTPS means traffic will flow through TCP port 443, a port commonly used for Web access. Secure Sockets Layer (SSL) provides transport-level security with enhanced key negotiation, encryption, and integrity checking.
QUESTION 65
You have a computer that runs Windows 7.
You need to record when an incoming connection is allowed through Windows firewall.
What should you do?
A. In Local Group Policy, modify the audit policy.
B. In Local Group Policy, modify the system audit policy.
C. From the Windows Firewall with Advanced Security properties, set the logging settings to Log successful
connections.
D. From the Windows Firewall with Advanced Security properties, set the Data Protection (Quick Mode) IPSec
settings to Advanced.
Answer: C
Explanation:
Customize Logging Settings for a Firewall Profile
Windows Firewall with Advanced Security can be configured to log events that indicate the successes and failures of its processes. The logging settings involve two groups of settings: settings for the log file itself and settings that determine which events the file will record. The settings can be configured separately for each of the firewall profiles. You can specify where the log file will be created, how big the file can grow, and whether you want the log file to record information about dropped packets, successful connections, or both. Log successful connectionsUse this option to log when Windows Firewall with Advanced Security allows an inbound connection. The log records why and when the connection was formed. Look for entries with the word ALLOW in the action column of the log.
QUESTION 66
Your company has a server named Server1 that runs Windows Server 2008. Server1 is a Windows Server Update Services (WSUS) server. You have a computer named Computer1
that runs Windows 7. Computer1 is configured to obtain updates from Server1.
You open the WSUS snap-in on Server1 and discover that Computer1 does not appear.
You need to ensure that Computer1 appears in the WSUS snap-in. What should you do?
A. On Server1, open Windows Update then select Check for updates.
B. On Server1, run Wsusutil.exe and specify the /import parameter.
C. On Computer1, open Windows Update and then select Change settings.
D. On Computer1, run Wuauclt.exe and specify the /detectnow parameter.
Answer: D
Explanation:
wuauclt.exeThe wuauclt utility allows you some control over the functioning of the Windows Update Agent. It is updated as part of Windows Update.Detectnow OptionBecause waiting for detection to start can be a time-consuming process, an option has been added to allow you to initiate detection right away. On one of the computers with the new Automatic
Update client installed, run the following command at the command prompt:
wuauclt.exe /detectnow
QUESTION 67
You have a computer that runs Windows 7. Windows Update settings are configured as shown in the exhibit. (Click the Exhibit button.)
You discover that standard users are never notified when updates are available.
You need to ensure that standard users are notified when updates are available.
What should you do?
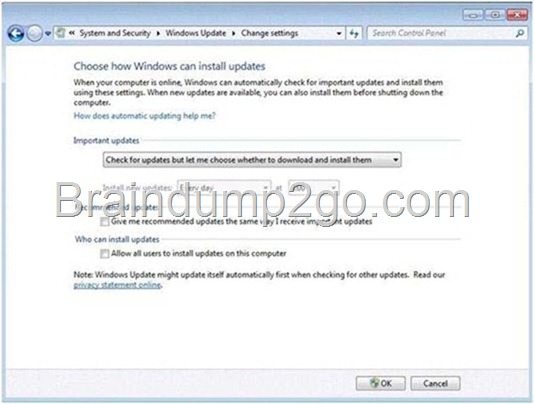
A. Select Allow all users to install updates on this computer.
B. Specify an intranet Microsoft update service location in Group Policy.
C. Change the Startup Type for the Windows Update service to Automatic.
D. Select Give me recommended updates the same way I receive important updates.
Answer: A
Explanation:
Change how Windows installs or notifies you about updates You can set Windows to automatically install important and recommended updates or to install important updates only. Important updates provide significant benefits, such as improved security and reliability. Recommended updates can address noncritical problems and help enhance your computing experience. Optional updates are not downloaded or installed automatically. If you don’t want updates to be installed automatically, you can choose to be notified when updates apply to your computer instead. Then, you can download and install them yourself, or you can set Windows to automatically download updates, and then notify you so you can install them yourself. Here’s how to change how Windows installs or notifies you about updates:
1. Click to open Windows Update.
2. In the left pane, click Change settings.
3. Under Important updates, click one of the following:
4. To schedule your automatic updates, next to Install new updates, select the day and time you want updates to occur. – Install updates automatically (recommended)
– Download updates but let me choose whether to install them
– Check for updates but let me choose whether to download and install them
– Never check for updates (not recommended)
5. To get recommended updates for your computer, under Recommended updates, select the Give me recommended updates the same way I receive important updates check box.
6. To allow anyone using the computer to make updates, select the Allow all users to install updates on this computer check box. This applies only to updates and software that are installed manually; automatic updates will be installed regardless of the user.
7. Click OK. If you’re prompted for an administrator password or confirmation, type the password or provide confirmation.
QUESTION 68
You have a computer that runs Windows 7.
Your computer’s disk configuration is shown in the exhibit.
(Click the Exhibit button.)
You need to ensure that you can create a striped volume on the computer.
What should you do?
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/4ea7ff376fbe_D67C/clip_image0024_thumb.jpg)
A. Add an additional hard disk.
B. Convert all disks to dynamic disks.
C. Install a digitally-signed disk driver.
D. Set the Startup Type of the Virtual Disk Service (VDS) to Automatic.
Answer: B
Explanation:
A striped volume is a dynamic volume that stores data in stripes on two or more physical disks. Data in a striped volume is allocated alternately and evenly (in stripes) across the disks. Striped volumes offer the best performance of all the volumes that are available in Windows, but they do not provide fault tolerance. If a disk in a striped volume fails, the data in the entire volume is lost.
You can create striped volumes only on dynamic disks. Striped volumes cannot be extended.
You can create a striped volume onto a maximum of 32 dynamic disks.
Backup Operator or Administrator is the minimum membership required to complete the actions below.
Creating a striped volume
Using the Windows interface
Using a command line
To create a striped volume using the Windows interface In Disk Management, right-click the unallocated space on one of the dynamic disks where you want to create the striped volume, and then click New Striped Volume….
Follow the instructions on your screen.
To create a striped volume using a command line
Open a command prompt and type diskpart.
At the DISKPART prompt, type list disk. Make note of the number of the disk where you want to create a striped volume.
At the DISKPART prompt, type create volume stripe [size=<size>] [disk=<disknumber>[,[<seconddisknumber>,
…]].
QUESTION 69
You have a computer that runs Windows 7. The computer is configured to automatically download and install updates. You install Microsoft Office 2007.
You need to ensure that service packs for Office are automatically installed.
What should you do?
A. From Windows Update, select Restore hidden updates.
B. From Windows Update, select Get updates for other Microsoft products.
C. Create a folder named Updates in C:\Program Files\Microsoft Office. Install the Office Update Inventory
Tool into the Updates folder.
D. Download and install the Office 2007 administrative template and disable the Block updates from the Office
Update Site from applying policy.
Answer: B
Explanation:
Use Windows Update to Check for Updates to other Microsoft Products By default, Windows Update can download and install updates for Windows 7 and features that are part of the operating system (such as Internet Explorer). You can also merge the functionality of Microsoft Update–a service for managing updates to Microsoft Office and several other Microsoft products–into Windows Update so that you no longer need to visit Office Online to get updates.If you do not already have Windows Update integrated with Microsoft Update, you will see the message “Get updates for other Microsoft products” on the Windows Update home page. To enable checking for other products, click the Find Out More option shown beside this message. This will take you to the Microsoft Update site for some quick installation steps. You only need to do this once. Thereafter, the Windows Update home page will indicate that you receive updates “For Windows and other products from Microsoft Update.”
QUESTION 70
You need to uninstall a Windows update from a computer that runs Windows 7. Which Control Panel item should you use?
A. Administrative Tools
B. Programs and Features
C. Sync Center
D. Troubleshooting
Answer: B
Passing Microsoft 70-680 Exam successfully in a short time! Just using Braindump2go’s Latest Microsoft 70-680 Dump:
http://www.braindump2go.com/70-680.html