QUESTION 91
Select the correct statement about Secure Internal Communications (SIC) Certificates. SIC Certificates:
A. Increase network security by securing administrative communication with a two-factor challenge
response authentication.
B. Uniquely identify machines installed with Check Point software only. They have the same function as
RSA Authentication Certificates.
C. Are for Security Gateways created during the Security Management Server installation.
D. Can be used for securing internal network communications between the Security Gateway and an
OPSEC device.
Answer: D
QUESTION 92
You need to plan the company’s new security system. The company needs a very high level of security and also high performance and high throughput for their applications. You need to turn on most of the integrated IPS checks while maintaining high throughput. What would be the BEST solution for this scenario?
A. You need to buy a strong multi-core machine and run R70 or later on SecurePlatform with CoreXL
technology enabled.
B. Bad luck, both together can not be achieved.
C. The IPS does not run when CoreXL is enabled.
D. The IPS system does not affect the firewall performance and CoreXL is not needed in this scenario.
Answer: A
QUESTION 93
You need to back up the routing, interface, and DNS configuration information from your R75 SecurePlatform Security Gateway. Which backup-and-restore solution do you use?
A. SecurePlatform backup utilities
B. upgrade_export and upgrade_import commands
C. Database Revision Control
D. Manual copies of the $FWDIR/conf directory
Answer: A
QUESTION 94
What information is provided from the options in this screenshot?
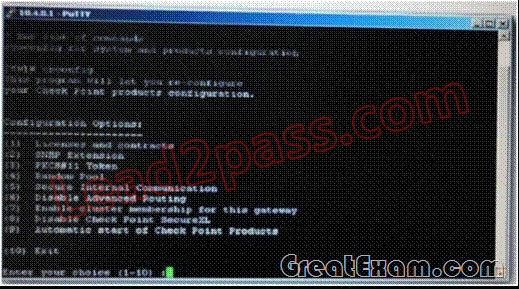
(i)Whether a SIC certificate was generated for the Gateway
(ii)Whether the operating system is SecurePlatform or SecurePlatform Pro
(iii)Whether this is a standalone or distributed installation
A. (i), (ii) and (iii)
B. (i) and (iii)
C. (i) and (ii)
D. (ii) and (iii)
Answer: D
QUESTION 95
Peter is your new Security Administrator. On his first working day, he is very nervous and sets the wrong password three times. His account is locked. What can be done to unlock Peter’s account? Give the BEST answer.
A. You can unlock Peter’s account by using the command fwm unlock_admin -u Peter on the Security
Gateway.
B. It is not possible to unlock Peter’s account. You have to install the firewall once again or abstain from
Peter’s help.
C. You can unlock Peter’s account by using the command fwm lock_admin -u Peter on the Security
Management Server.
D. You can unlock Peter’s account by using the command fwm unlock_admin -u Peter on the Security
Management Server.
Answer: C
QUESTION 96
Which CLI command verifies the number of cores on your firewall machine?
A. fw ctl pstat
B. fw ctl core stat
C. fw ctl multik stat
D. cpstat fw -f core
Answer: C
QUESTION 97
Before upgrading SecurePlatform, you should create a backup. To save time, many administrators use the command backup. This creates a backup of the Check Point configuration as well as the system configuration.
An administrator has installed the latest HFA on the system for fixing traffic problem after creating a backup file. There is a mistake in the very complex static routing configuration. The Check Point configuration has not been changed. Can the administrator use a restore to fix the errors in static routing?
A. The restore can be done easily by the command restore and selecting the appropriate backup file.
B. A backup cannot be restored, because the binary files are missing.
C. The restore is not possible because the backup file does not have the same build number (version).
D. The restore is done by selecting Snapshot Management from the boot menu of SecurePlatform.
Answer: A
QUESTION 98
Which operating systems are supported by a Check Point Security Gateway on an open server?
A. Check Point SecurePlatform and Microsoft Windows
B. Sun Solaris, Red Hat Enterprise Linux, Check Point SecurePlatform, IPSO, Microsoft Windows
C. Check Point SecurePlatform, IPSO, Sun Solaris, Microsoft Windows
D. Microsoft Windows, Red Hat Enterprise Linux, Sun Solaris, IPSO
Answer: A
QUESTION 99
Another administrator accidentally installed a Security Policy on the wrong firewall. Having done this, you are both locked out of the firewall that is called myfw1. What command would you execute on your system console on myfw1 in order for you to push out a new Security Policy?
A. fw dbloadlocal
B. fw unloadlocal
C. cpstop
D. fw ctl filter
Answer: B
QUESTION 100
How is wear on the flash storage device mitigated on appliance diskless platforms?
A. A RAM drive reduces the swap file thrashing which causes fast wear on the device.
B. The external PCMCIA-based flash extension has the swap file mapped to it, allowing easy replacement.
C. Issue FW-1 bases its package structure on the Security Management Server, dynamically loading when
the firewall is booted.
D. PRAM flash devices are used, eliminating the longevity.
Answer: A
If you want to pass the Check Point CCSA 156-215.75 exam sucessfully, recommend to read latest Check Point CCSA 156-215.75 Test Engine full version.